Risk Assessments
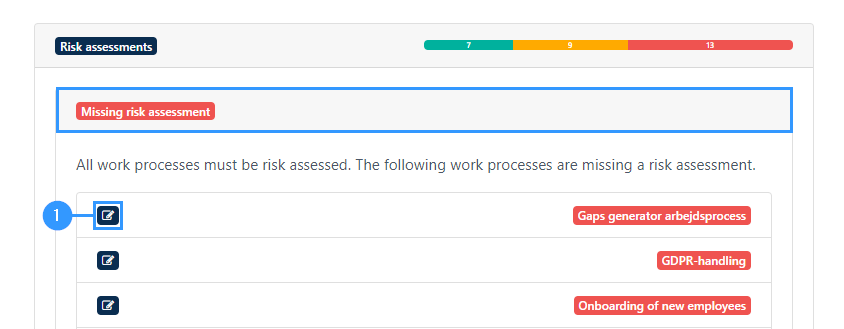
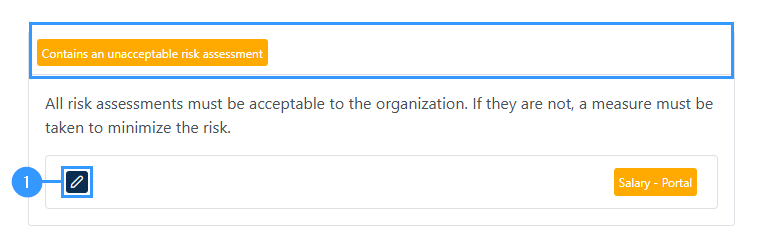
When clicking on this bar, you will be able to see the gaps within the category.
All work processes must be risk assessed. The following work processes are missing a risk assessment.
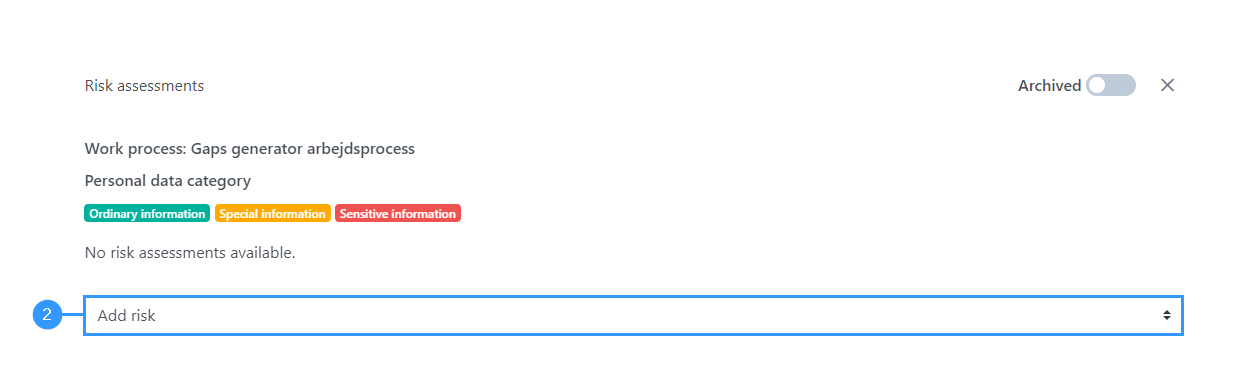
To remove the gap, you must create a risk assessment.
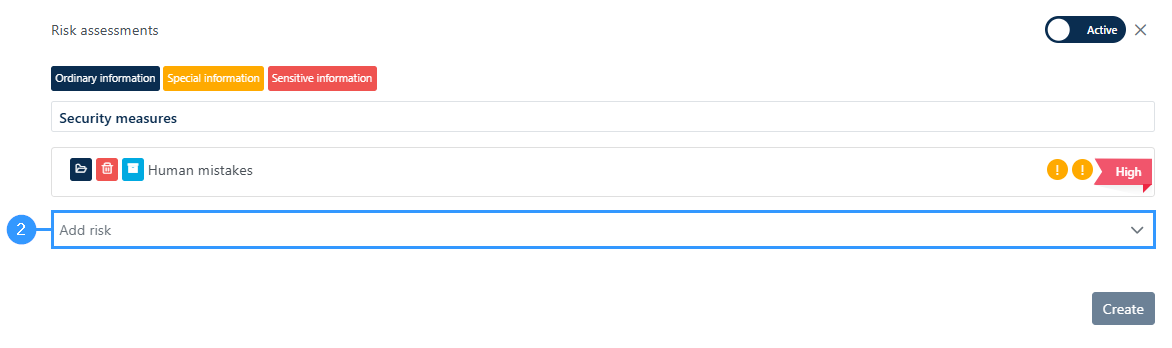
All risk assessments must be acceptable to the organization. If they are not, a measure must be taken to minimize the risk.
Adresse
GapSolutions A/S
Uraniavej 6
DK-8700 Horsens
CVR
CVR-nr. 38582356
Telefon
Salg & administration
(+45) 8844 0808
Helpline & konsulenter
(+45) 2199 0808
E-mail
Kontakt@gapsolutions.dk
Support@gapsolutions.dk
Vi bruger udelukkende tekniske cookies på vores hjemmeside. For yderligere information se vores Cookiepolitik.
Vi er ISO 27001-certificeret og ISAE 3000-auditeret.