IT systems / information assets
IT systems / information assets are programs and assets that contain information. It can be software, as well as it can be physical things like laptops, external hard drives, etc.
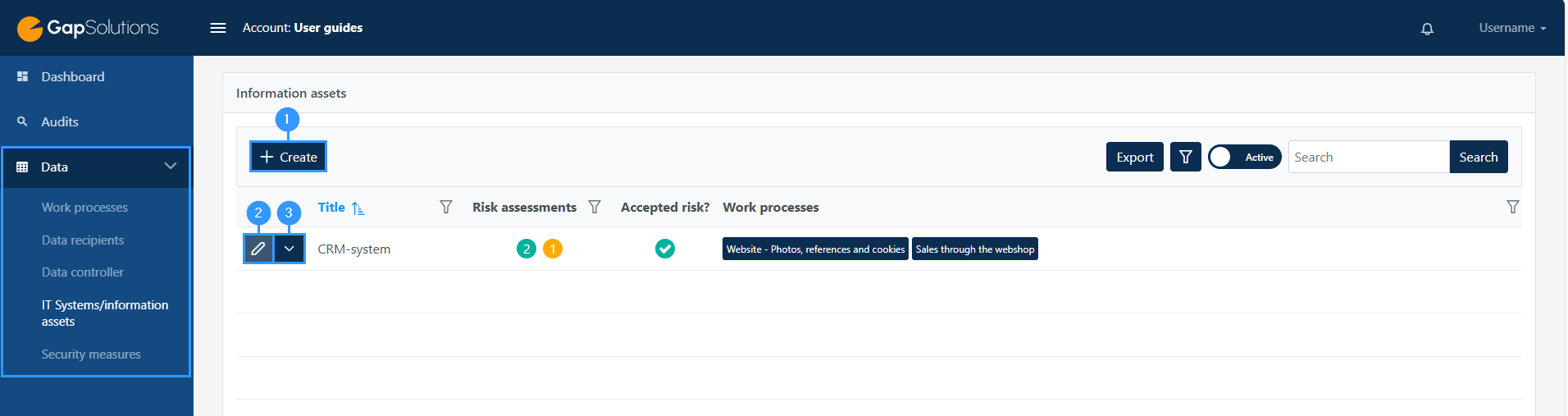
When clicking “create” (1) in the left corner in the overview of IT systems/information assets or “edit” (2) next to an IT system/information asset, you will open a longer form.
If you want to export, archive or delete, press (3) in the image below:
In this form, there will be some different characters at the fields:
1. Red exclamation mark – Gap
In the front of the field, you will be able to see a red exclamation mark. The red exclamation mark is an expression of a gap. A gap can also be indicated with a yellow exclamation mark.
2. Blue infobox
–When you click on the little ’i’, an information box with further information about what you should specify in every field will show. The information box can also contain a deepening explanation on the meaning of the choices you can choose.
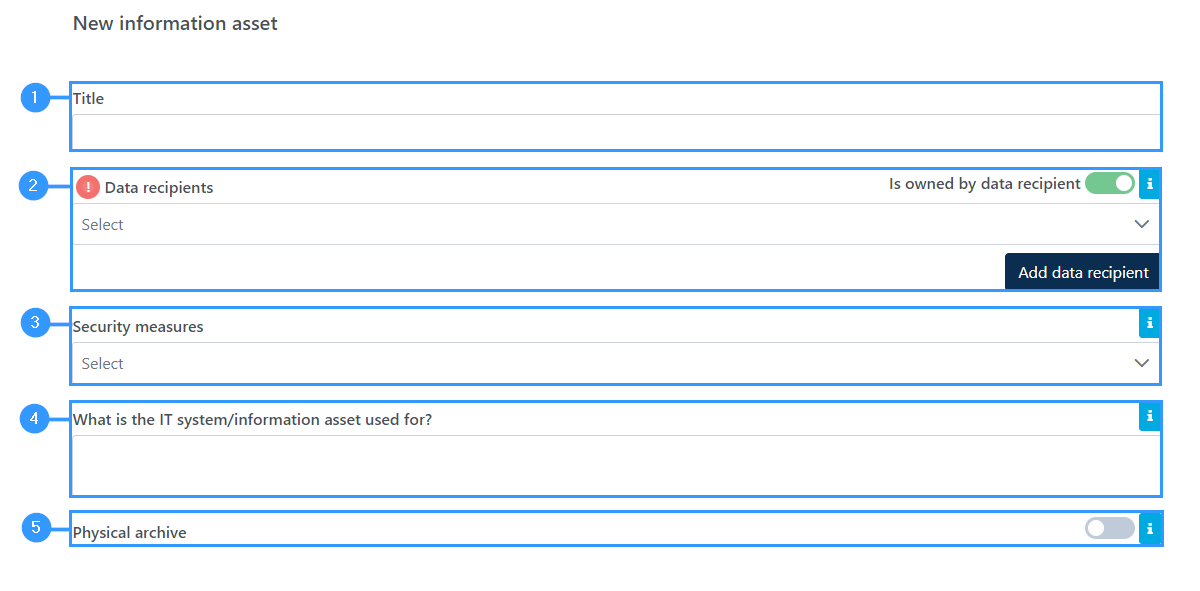
1. Title
-Here you need to specify the title of the IT system / information asset used.
2. Data recipients
-Here it can be specified which data recipient owns the IT system. You can do this by clicking on the line and a list of all data recipients will appear.
If a data recipient is missing, you can click on ‘Add data recipient’ in the bottom right corner, after which a form will open for adding a data recipient.
This is primarily relevant for systems where data is moved out of the company, e.g. via apps, hosting, cloud services or email servers.
3. Security measures
-Here all the security measures applicable to the IT system / information asset are indicated. Both technical and organisational security measures must be indicated.
4. What is the IT system/information asset used for?
-Briefly describe what the IT system/information asset is used for in the company.
5. Physical archive
-Here you need to specify whether it is a physical archive. Your choice in this field determines the form’s following fields.
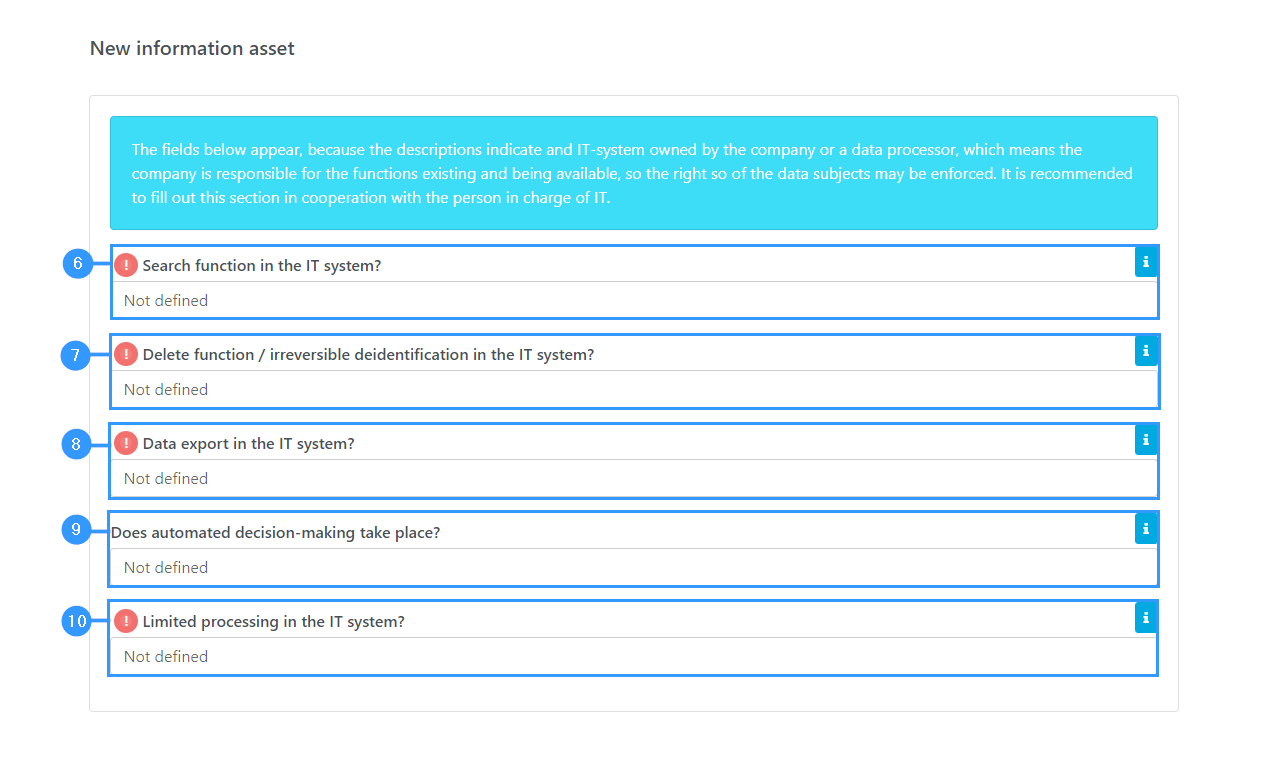
6. Search function in the IT system?
-Can the IT system identify personal data about a specific person? Clicking on this field will make various choices you can make.
7. Delete function / irreversible deidentification in the IT system?
-Is it possible to delete data in the system? Clicking on this field will make various choices you can make.
8. Data export in the IT system?
-Is it possible to export data out of the system in a structured, commonly used and machine-readable format? Clicking on this field will make various choices you can make.
9. Does automated decision-making take place?
-You must indicate here whether automated decision-making – including profiling – takes place in the IT system. Clicking on this field will make various choices you can make.
10. Limited processing in the IT system?
-Can the IT system in question limit processing to storage only in the cases specified in the information box at the point? Clicking on this field will make various choices you can make.
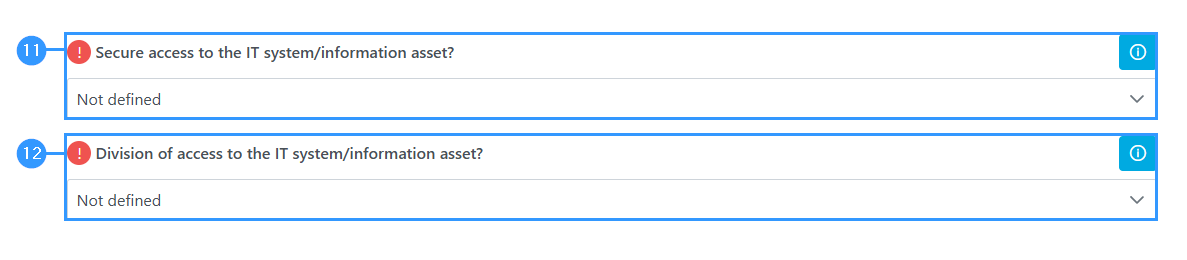
11. Secure access to the IT system/information asset?
-Here you must indicate whether there is secure access to the IT system / information asset.
It is a requirement that there are appropriate technical measures to protect data against unauthorized access, including, for example, strong passwords or multi-factor authentification login.
12. Division of access to the IT system/information asset?
-You must then specify whether there is division of access in the IT system / information asset – whether access to data in the system can be divided, for example, based on the user’s roles and rights. Clicking on this field will show the choices you can make.
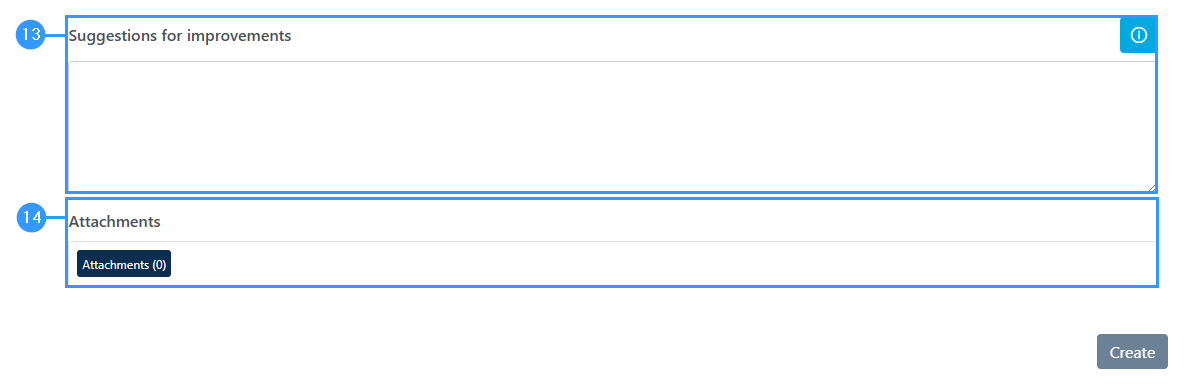
13. Suggestions for improvements
-At the end of the form, at this field, you can provide suggestions for improvements.
14. Attachments
-At this field you can upload files by clicking on ‘attachments’, where the option to attach files will open.
Adresse
GapSolutions A/S
Uraniavej 6
DK-8700 Horsens
CVR
CVR-nr. 38582356
Telefon
Salg & administration
(+45) 8844 0808
Helpline & konsulenter
(+45) 2199 0808
E-mail
Kontakt@gapsolutions.dk
Support@gapsolutions.dk
Vi bruger udelukkende tekniske cookies på vores hjemmeside. For yderligere information se vores Cookiepolitik.
Vi er ISO 27001-certificeret og ISAE 3000-auditeret.