Transfer impact assessment – TIA
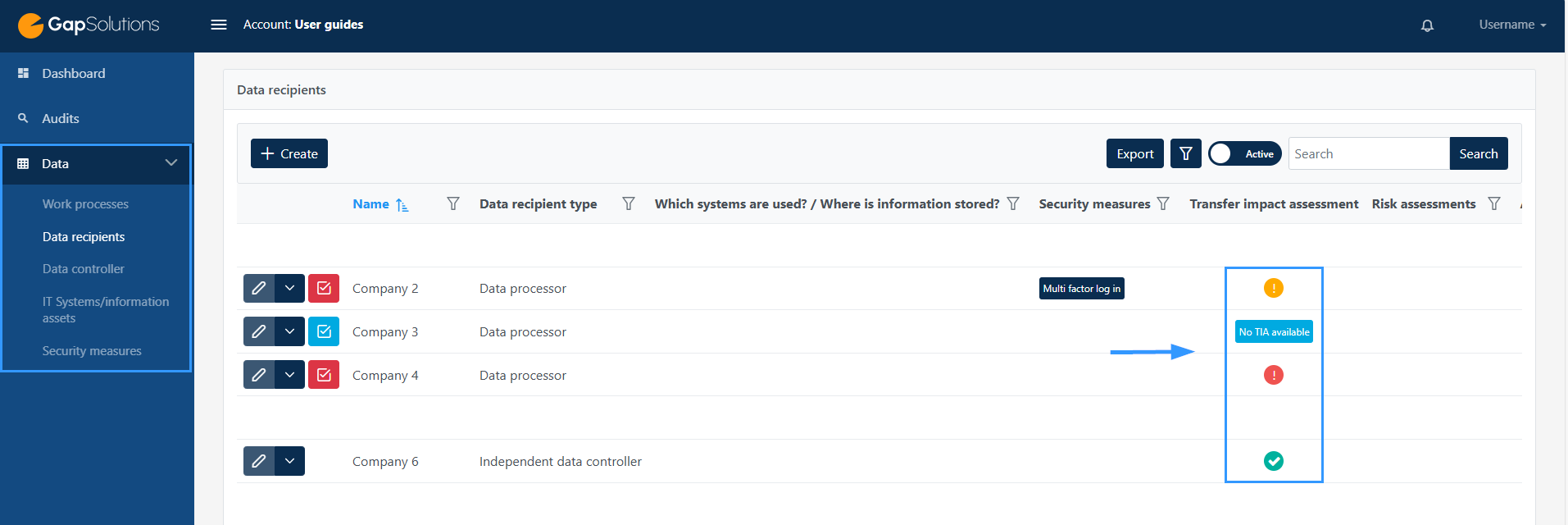
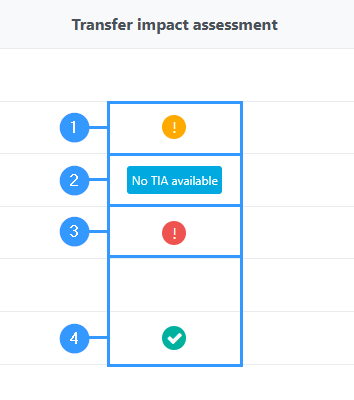
When you create a data recipient, you must answer whether a data recipient is in an insecure third country. If a data recipient is in an insecure third country, it is necessary to complete a TIA. When working with data recipients, the column ‘Transfer impact assessment’ will show whether a risk assessment of data transfers to insecure third countries has been established. This will only be available to data recipients who are set to be in an insecure third country.
1. A yellow exclamation mark
-Indicates that a TIA has been filled in, but that the risk is medium.
2. No TIA available
-This blue text box will appear in cases where a TIA remains to be filled in.
3. A red exclamation mark
-Indicates that the risk is very high.
4. The green check mark
-Indicates that a TIA has been filled in and that the risk is either low or very low.
The initial filling of the formula
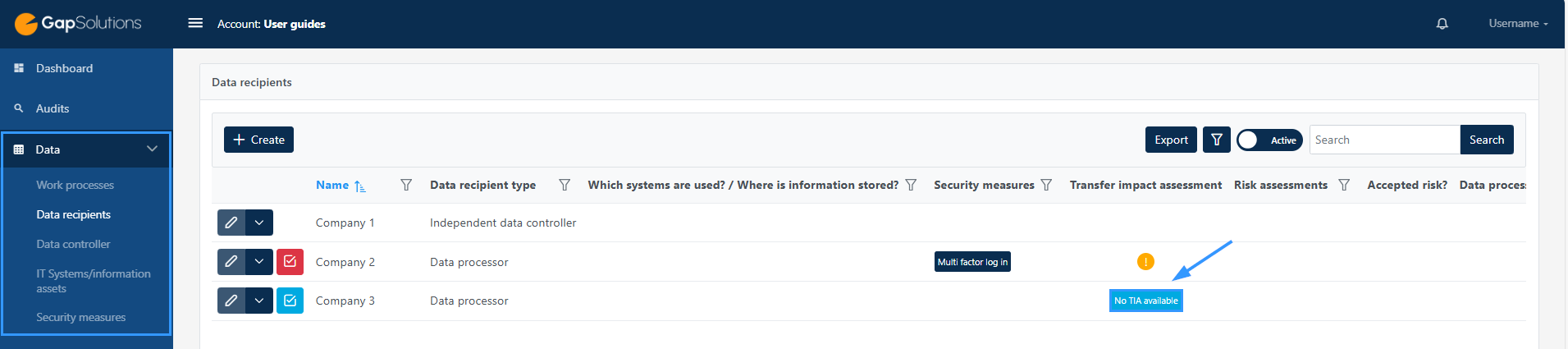
In the example below, it is assumed that the data recipient type is a data processor and the insecure third country that takes place transfer to is; the United States.
To open the form for the specifik assessment press “No TIA available” as shown in the image above.
1. TIA: introduction
-This field is an introduction to the TIA to be completed. By clicking on this, you can read about why a TIA should be prepared and what a TIA is.
2. Country
-Here you will be able to see which unsafe third country data is being transferred to. The country that is specified is the one you have filled in when you have created a data recipient and stated that there is a transfer to an unsafe third country.
3. Work processes
-This lists all the work processes that either use the data recipient directly or indirectly. Any work processes created where the data recipient has been entered will automatically appear in this form. It is possible to click on the field, which will open information about the legal basis for each work process as well as what types of information are used for each work process.
4. Personal data category
-In this field you will find an overview of all the types of information used in connection with the data recipient. By clicking on the individual types of information, you will open a field where you can see exactly what information within the different categories is used.
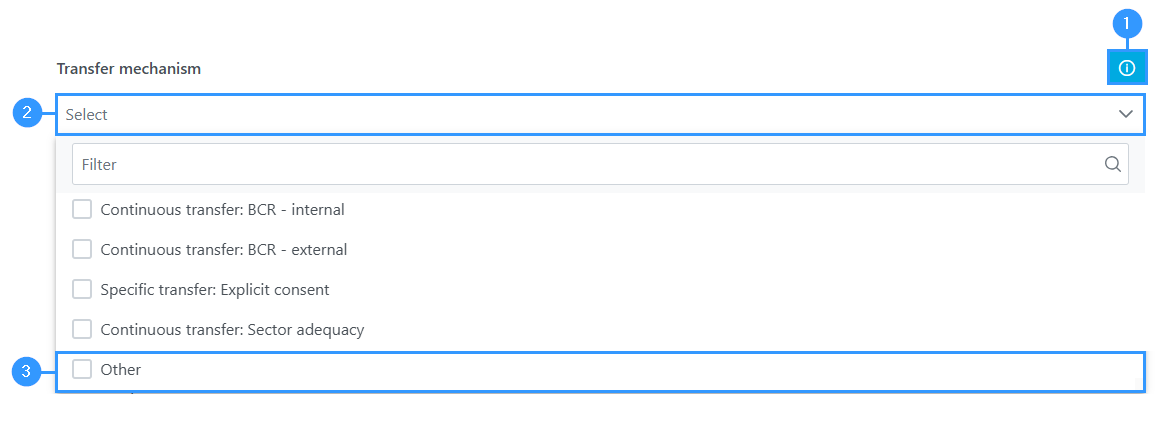
Transfer mechanism
You should now select the transfer basis. By clicking on the field, you can choose from the most common bases, but you can also select ‘other’, which will add a field where you will be able to choose from the other, less used options.
1. Information box
-You can click here to read more about each of the transfer bases.
2. Select
-Click here to see an overview of the most common transfer bases.
3. Other
-Click here if you want to see other transfer bases.
Duration of the transfer
Duration of the transfer
The duration you must specify covers how long the transferred information will be outside the scope of the GDPR.
It varies greatly depending on whether it is a short processing such as email addresses for mail sending or long-term storage, such as in connection with hosting services.
This duration can be described in several ways. You can choose to set an end date when all data is deleted or withdrawn, or you can specify the criteria for when data is deleted.
If data is stored / processed indefinitely outside the scope of the GDPR, it is recommended to reconsider this and explore other possible solutions.
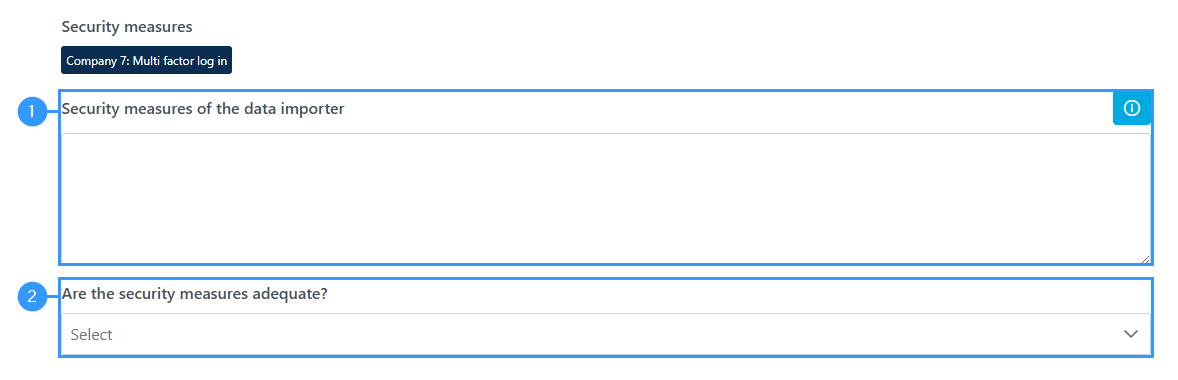
Security measures
1. Security measures of the data importer
-This field in the form will show the security measures associated with the data recipient directly or in connection with some of the IT systems or work processes to which the data recipient is connected directly.
This overview will be autogenerated from the other mappings created in the portal. This means that these security measures do not necessarily cover all the security measures that apply to the individual data recipient. Based on this, you need to decide whether the security measures are sufficient to secure the data you send to the data recipient.
2. Are the security measures adequate?
-In this field you must clarify if the security measures are adequate.
Jurisdiction
Jurisdiction
-Here you need to specify which legislation in the receiving country may cause problems for the protection of data subjects’ rights.
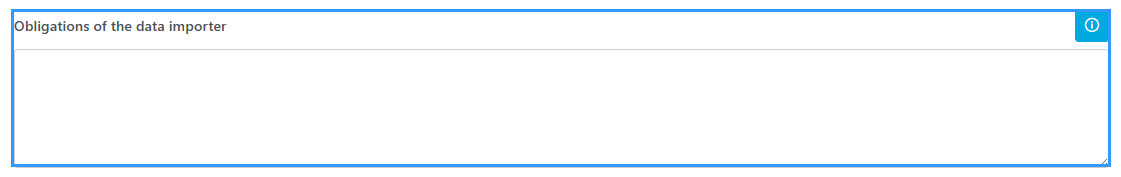
Obligations of the data importer
Obligation of the data importer
-Describe whether the data importer is obligated to notify the data exporter about unauthorised attempts at access as well as legally binding demands for disclosure from authorities.
This must be assessed in the context of whether the data subject and the data exporter can be said to have sufficient means to seek redress. Assessing the sufficiency must be based on whether local authorities can demand disclosure and also require the data importer to not give notice to the data exporter about such disclosure. If this is possible, the access to redress is not sufficient / adequate.
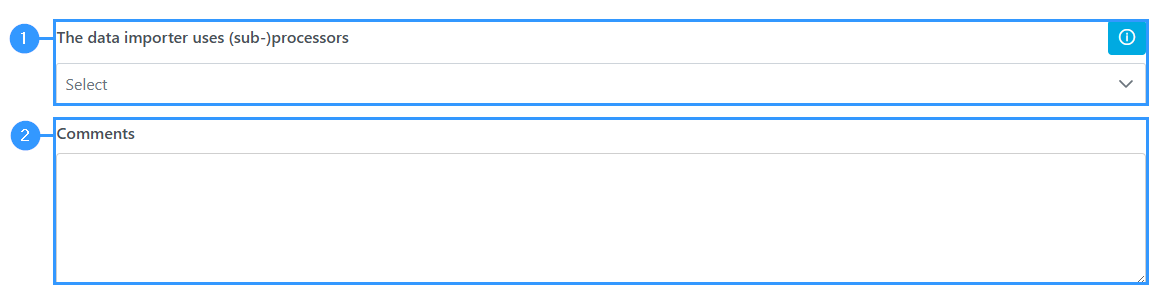
The data importer uses (sub-)processors
1. The data importer uses (sub-)processors
-Here you must indicate whether the data importer uses sub-processors. The use of sub-processors can complicate the process of making an adequate assessment of the real risks.To achieve the best possible result, it must be recorded whether the data importer uses sub-processors.
2. Comments
-In this field, it can be described which sub-processors are involved, which countries they are in and how this affects the risk assessment in this TIA. In the case of many sub-processors, it is not necessary to mention them individually, but simply note how the large number affects the risk assessment.
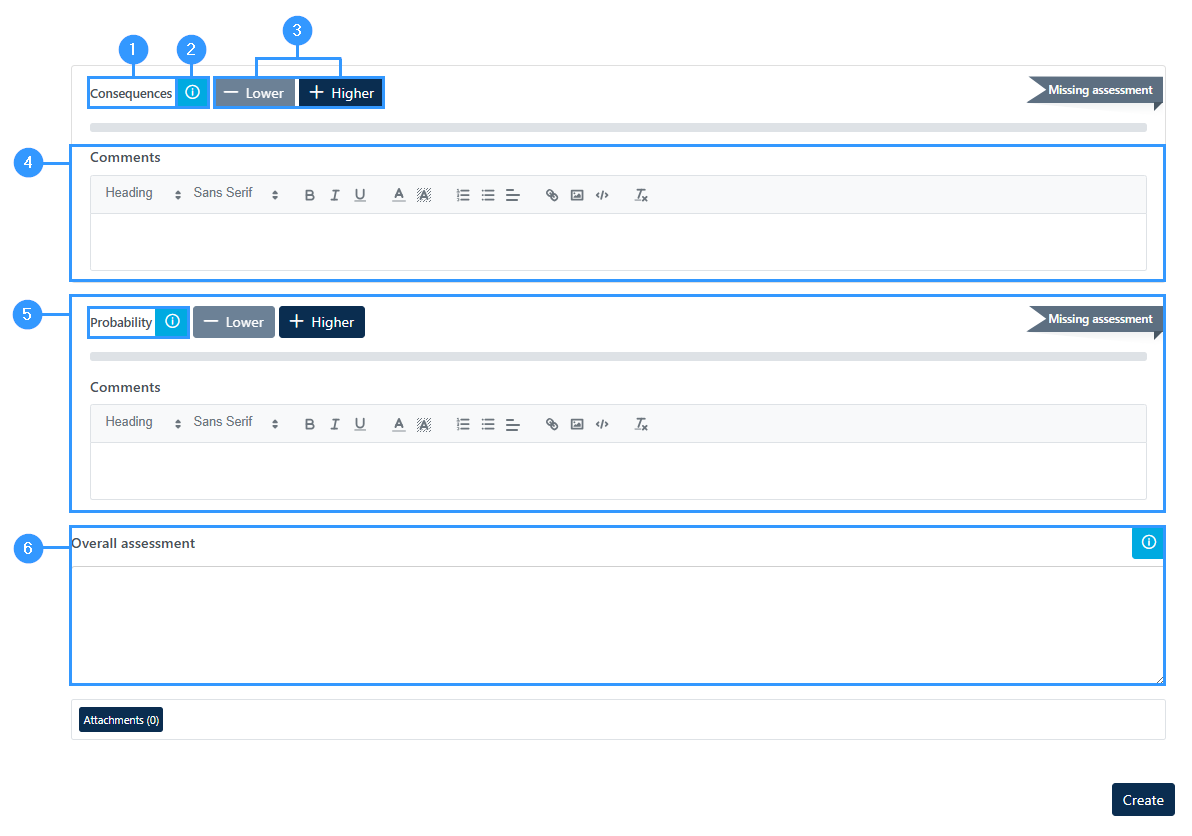
Risk assessment
A risk assessment of the data transfer must now be carried out.
1. Consequences
-To see how you assess the consequences, you can click on section 2, where a detailed explanation of what the different levels reflect is explained in more detail.
2. Information box
-Click this icon to open an in-depth field. The same applies to the calculation of the probability below.
3. – Lover / + Higher
Use these buttons to set the level of consequences. When you click on the two buttons, you will be able to see the level you set, where the example says ‘missing assessment’. The same applies to the calculation of probability.
4. Comments
-Here is a free text field where you can write comments on the completion of the field.
5.Probability
-Here you need to evaluate the likelihood that unauthorized persons can access the personal data. The general procedures for processing personal data must be taken into account. If it is easy to access the information for unauthorized persons, it must be considered that the probability is high.
6. Overall assessment
In this field, an overall assessment of the risk is made.
The TIA must lead to a conclusion based on the above fields. Is it justifiable to continue the transfer of data to the data importer or not?
The overall assessment is autogenerated based on how the above two parts of the risk assessment are assessed.
Adresse
GapSolutions A/S
Uraniavej 6
DK-8700 Horsens
CVR
CVR-nr. 38582356
Telefon
Salg & administration
(+45) 8844 0808
Helpline & konsulenter
(+45) 2199 0808
E-mail
Kontakt@gapsolutions.dk
Support@gapsolutions.dk
Vi bruger udelukkende tekniske cookies på vores hjemmeside. For yderligere information se vores Cookiepolitik.
Vi er ISO 27001-certificeret og ISAE 3000-auditeret.