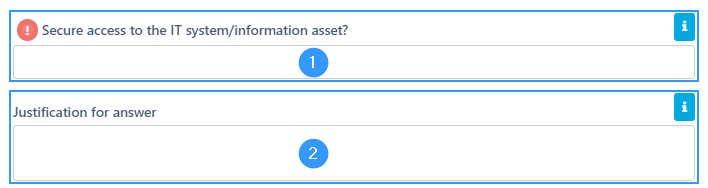
Secure access to the IT system / information asset?
When clicking on this bar, you will be able to see the gaps within the category.
Access to the system must be protected by appropriate technical measures. This gap is removed by selecting “Yes” in the system description when user accesses are regulated with the appropriate measures (1).
It must be justified why ‘Secure access to the IT system/information asset’ is not relevant (2).
Address
GapSolutions A/S
Uraniavej 6, 1.
DK-8700 Horsens
CVR
CVR-nr. 38582356
Phone
Sales & administration
(+45) 8844 0808
Helpline & consultants
(+45) 2199 0808
Cookiepolicy
Privacy policy